The source code for Cyberpunk 2077 has apparently leaked to the Internet -apkrig
CD Projekt’s servers were attacked by hackers at the beginning of February this year. The developers informed themselves immediately after the attack and also shared a message they found on their servers after the incident. The hackers demanded a ransom not only for returning the copied data, but also for unlocking them directly on the Project CD server. Otherwise, they threatened to publish or sell the acquired files, which included the source code of Cyberpunk 2077, Sorcerer 3, its supposed next-gen version with ray tracing, RedEngin source code and many documents concerning the operation of the company and its investors. But because the developers did not want to negotiate with the attackers, a report appeared after a few days that the data had gone to auction for a starting price of $ 1 million, or for six times that amount in an immediate sale. However, the auction was to fall out when hackers someone offered a sufficiently high amount on the condition that the data would never be disseminated to the public. However, this brings us to the current report, which states that the condition has been lifted and that access to the data described above should be available to anyone who pays $ 10,000.
The DataBreaches portal came up with the information, which first points to a change in the strategy of the Babuk platform, through which the stolen data escapes to the public via the dark web. “Babuk is changing its approach – we will no longer lock your data on servers, but we will take it directly from you. You will receive a warning, and if you do not contact us, we will make a statement, “hackers should tell companies from among the potential targets of further attacks. Subsequently, the representatives of the Babuk group transformed their website into the Payload.bin platform and added that they will publish stolen data through it, whether they obtained it themselves or in these cases only serve as a distributor for lesser-known groups that do not have their own blog or place from where could offer data to interested parties. And to attract attention, they promised one big one leak, which will go into the world through Payload.bin – stolen but password-protected data from the CD Project from the HelloKitty group, violating the condition described above, thanks to which the original auction was closed.
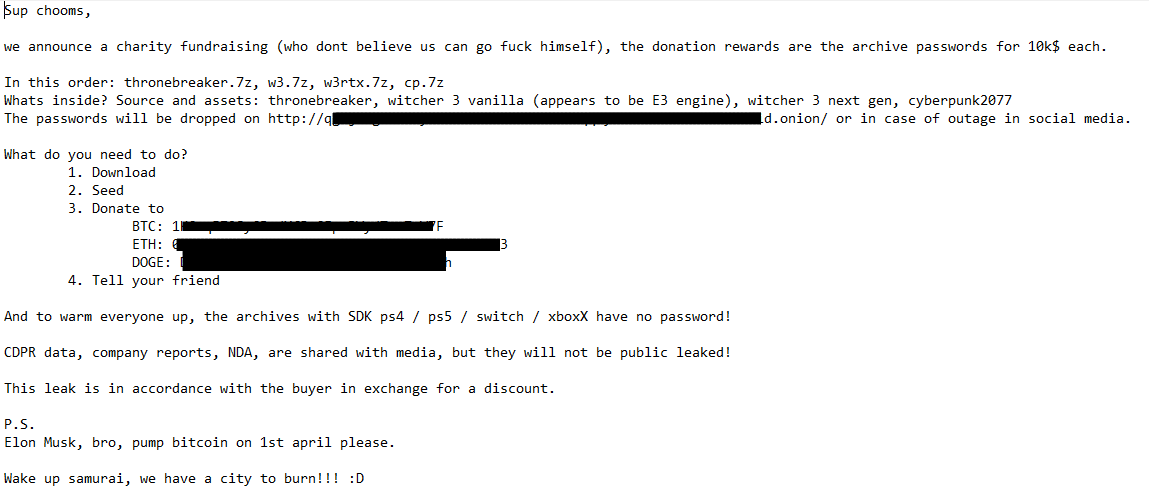
Passwords were offered gradually from the source code to the game Thronebreaker: The Witcher Tales, through The Sorcerer 3 and its version with ray tracing, to Cyberpunk 2077.
Furthermore, the incident is discussed on the Reseter portal, where a user with the nickname delete13245 shared a screenshot of the mentioned group of hackers. They inform in it about raising money for charity through the password to the data packages from the Project CD, which can be obtained by anyone who pays $ 10,000 in Bitcion, Ethereum or Dogecoin cryptocurrencies. Passwords were offered gradually from the source code to the game Thronebreaker: The Witcher Tales, through Sorcerer 3 and its version with ray tracing, to Cyberpunk 2077. As for internal information about the company, the HelloKits did not even offer it through Payload.bin and to this account they only stated that they had sent this part of the data to the media. Finally, they add an explanation for why they want to publish the data when the conditions of the auction were set differently – the reason is to request a discount from the person who set the condition against payment four months ago. At the very end, however, comes an important note, through which the whole case moves to a slightly different level. HelloKitty is asking Elon Musek from a distance to make a contribution on social networks on April 1 pumped out the price of Bitcion, so it is very likely that the source code was sold in March.
 Source: Resetera
Source: ReseteraThe quoted thread on Resetera also features a user – jmga – who claims to have had access to the leaked data and confirms its authenticity, which is impossible to prove in any way at the level of Internet discussion. Therefore, the line about the associated releases of the SDK consoles PS4, PS5, Switch and Xbox Series X, which were on the Project CD servers and allegedly not protected by any other password in the password-protected archives, is much more interesting. Therefore, a debate has started on what this potentially means for the protection of new consoles in particular, but in reality, leakage – if it really happened – would not necessarily mean anything serious. The SDK itself does not yet open the way to exploits or possibilities hacknout console and the passionate debate on Resetera ended very quickly. As a result, the real problem remains “only” the leakage of game data and expectations of what can cause developers damage in the long run.